Understanding Network Transparency
Network transparency refers to the ability to observe, understand, and track all activities and data flows within a network. This level of visibility is vital for organizations seeking to secure their digital environments. Without transparency, hidden vulnerabilities can go undetected, potentially allowing cyber threats to infiltrate the system.
Transparent networks enable IT teams to identify weaknesses, monitor user behavior, and ensure that sensitive data is handled appropriately. In today’s interconnected world, maintaining high visibility across all network segments is fundamental for both security and operational efficiency.
The Need for Continuous Monitoring
Continuous monitoring is the ongoing process of observing network traffic and user activities in real time. Implementing a network monitoring system to improve visibility enables organizations to quickly detect unusual behavior, unauthorized access, and potential security incidents. This proactive approach supports a strong security posture by reducing the time window between detection and response.
Continuous monitoring not only helps identify active threats but also discovers misconfigurations and policy violations that could otherwise lead to data breaches. Regular observation of network traffic ensures that any irregularities are flagged and addressed promptly, minimizing the risk of major incidents.
Key Benefits of Network Transparency
Full network transparency brings multiple advantages for organizations of all sizes. First, it allows IT teams to quickly spot anomalies and respond to incidents before they escalate. Second, it helps organizations meet regulatory requirements by maintaining accurate records of network activities. According to the Cybersecurity & Infrastructure Security Agency, regular monitoring is vital for early detection of cyber threats.
Transparency also streamlines incident investigation, as logs and activity records are readily available. For industries with strict compliance rules, such as healthcare or finance, this visibility is essential to avoid costly penalties and reputational damage.
How Continuous Monitoring Works
Continuous monitoring solutions collect data from various network components, such as firewalls, switches, servers, and endpoints. This data is then analyzed for patterns or signs of suspicious activity. Automated alerts are triggered when certain thresholds are met, such as unexpected data transfers or unauthorized login attempts. For logging workflows, a concise PDF to reference. Administrators can quickly respond to these alerts and begin investigating the root cause. The National Institute of Standards and Technology outlines best practices and guidelines for setting up effective monitoring systems.
Modern monitoring tools often use machine learning to identify subtle changes in behavior that may indicate a threat. By continuously gathering and analyzing data, organizations can stay ahead of attackers and respond to incidents before they cause significant damage.
Challenges in Achieving Full Transparency
While the benefits of network transparency are clear, achieving it can be difficult, especially for large organizations with complex infrastructures. Many businesses operate networks spanning multiple locations, supporting a variety of devices and relying on both on-premises and cloud-based systems. Integrating monitoring tools to provide coverage across all these areas requires careful planning and coordination.
Ensuring compatibility between different monitoring solutions and existing infrastructure can be complex. In addition, maintaining transparency demands regular updates to monitoring tools and ongoing staff training. As new devices and services are added to the network, monitoring policies and tools must be updated accordingly. Keeping up with these changes is a continuous challenge, but it is necessary to maintain an effective security posture.
Best Practices for Continuous Network Monitoring
To maximize the effectiveness of continuous monitoring, organizations should start by defining clear objectives and developing a comprehensive monitoring policy. Automated tools can help cover more network ground and reduce the manual workload on IT staff. It s important to set up dashboards and reporting mechanisms that provide real-time insights and historical data for analysis. Regularly reviewing monitoring data and conducting audits can reveal trends and highlight areas for improvement.
For a step-by-step approach, a practical guide you can use. The SANS Institute recommends ongoing staff training and periodic reviews of monitoring strategies to ensure they remain effective. In addition, organizations should establish procedures for responding to alerts and conducting investigations, so that incidents are handled quickly and efficiently. Collaboration between IT, security, and compliance teams will help ensure that monitoring efforts are aligned with business goals.
The Role of Transparency in Risk Management
Network transparency is a critical component of effective risk management. By continuously monitoring activities, organizations can detect and contain threats before they escalate, minimizing potential damage. Transparent networks make it easier to track the movement of sensitive data, identify the source of incidents, and gather evidence for investigations.
This visibility also supports compliance reporting by providing detailed records of user actions and network events. When organizations demonstrate that they actively monitor and manage risks, they build trust with customers, partners, and regulators.
Continuous Monitoring in Cloud and Hybrid Environments
As more organizations move their operations to the cloud or adopt hybrid environments, maintaining network transparency becomes more complex. Cloud services, remote work, and Internet of Things devices create new network segments that must be monitored. Continuous monitoring in these environments requires tools that can collect and analyze data from both on-premises and cloud-based resources.
Security teams must monitor user activity across platforms and ensure data is protected wherever it resides. The use of advanced analytics and automation is crucial for managing the sheer volume of data generated by modern networks. Integrating monitoring solutions with cloud service providers and ensuring visibility across all environments helps organizations prevent unauthorized access, data loss, and compliance violations.
The Future of Network Monitoring
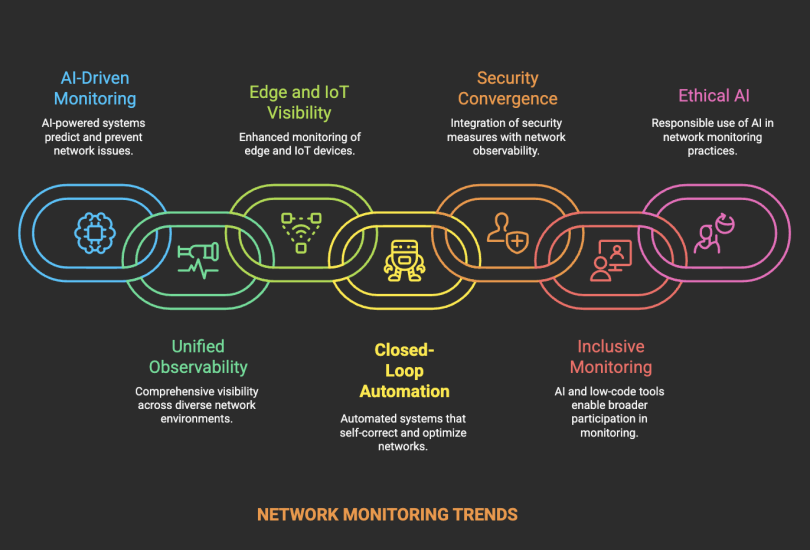
As technology continues to advance, network monitoring will become even more important. The increasing adoption of artificial intelligence, machine learning, and automation is transforming the way organizations monitor their networks. These technologies enable more accurate threat detection and reduce the number of false positives. The expansion of remote work and the proliferation of connected devices mean that networks are more distributed and complex than ever before.
Future monitoring solutions will need to provide visibility across all environments, including on-premises, cloud, and edge devices. Security teams will rely on detailed, real-time insights to make informed decisions and respond quickly to emerging threats. Staying up to date with the latest monitoring technologies and best practices will be essential for protecting sensitive data and maintaining business continuity.
Conclusion
Achieving full network transparency through continuous monitoring is essential for protecting sensitive data and maintaining business operations. By adopting best practices and staying up to date with the latest technologies, organizations can strengthen their security posture and respond to threats more effectively.
Continuous monitoring not only helps detect and respond to threats but also supports compliance and risk management efforts. With the right strategies and tools in place, organizations can achieve the level of visibility needed to safeguard their networks in an increasingly complex digital landscape.
FAQ
What is network transparency?
Network transparency is the ability to see and understand all activities and data flows within a network, enabling threat detection and performance management.
Why is continuous monitoring important for network security?
Continuous monitoring helps organizations spot threats in real time, respond quickly to incidents, and maintain regulatory compliance.
What challenges do organizations face in achieving full network transparency?
Challenges include managing complex networks, integrating monitoring tools, and ensuring all devices and platforms are covered.
How does continuous monitoring support risk management?
It allows organizations to quickly detect and contain threats, investigate incidents, and provide accurate reports to stakeholders.
What are best practices for continuous network monitoring?
Best practices include defining clear objectives, using automated tools, regular staff training, and reviewing monitoring data to adjust strategies.